[tab name=’News’]
Just the other day we told you about a new piece of malware that has been discovered by researchers called Flame. The malware was thought to be one of the most sophisticated malicious program ever created.
However, some of you may be aware of another piece of malware/cyber-weapon called Stuxnet. It was also a very well written and sophisticated and was tasked to spy on and subvert industrial systems, specifically PLCs (programmable logic controllers).
Researchers carrying out analysis of both pieces of malware are of the strong belief that they have been created by a state nation, instead of a cyber-criminal gang. And now, more information has been been another discovered which suggests that both Flame and Stuxnet creators cooperated at least once in the early development stages.
The new finding have been discovered by Kaspersky, who also originally discovered the Flame malware. Chief Security Expert Alexander Gostev said: “What we have found is very strong evidence that Stuxnet/Duqu and Flame cyber-weapons are connected,”.
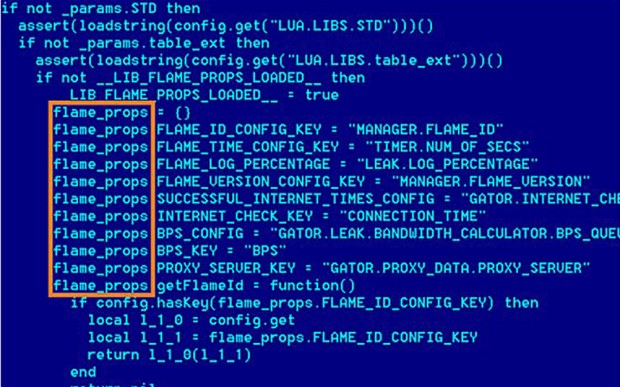
According to Kaspersky, a connection between the two pieces of malware exists in a special module known as ‘Resource 207’ which was present in the earliest known version of Stuxnet, discovered back in 2009. However, it was later removed in a revised version of Stuxnet that was found in the wild in 2010.
It would seem that ‘Resource 207’ used in Stuxnet has a lot in common with Flame malware, for example the names of mutual exclusive objects, the algorithm used for decryption along with a similar structure of file naming.
But, although there are a handful of similarities between Stuxnet and Flame, Mr Gostev is still pretty sure that both programs originated and were developed on completely different platforms.
“They each have different architectures with their own unique tricks that were used to infect systems and execute primary tasks. The projects were indeed separate and independent from each other.”
Let us know your thoughts on our comments below or via our @Gadget_Helpline Twitter page or Official Facebook group.
[/tab]
[end_tabset]